Trezor Login: Secure Access to Your Hardware Wallet
A secure Trezor Login is the gateway to managing your digital assets with confidence. Whether you are a beginner or an experienced investor, mastering the Trezor Login process ensures your private keys and funds remain safe within your hardware wallet.
Getting Started with Trezor Login
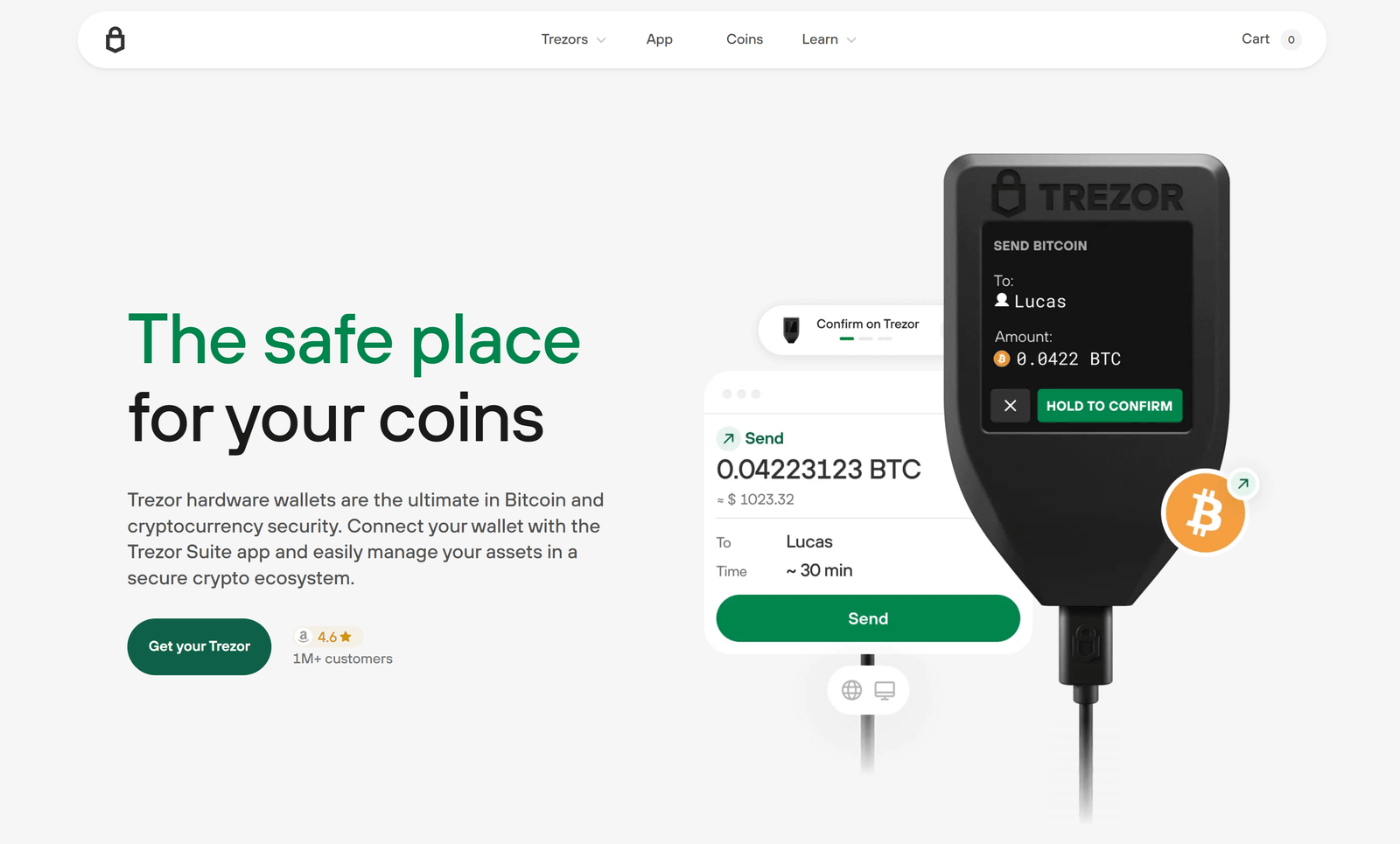
To begin a Trezor Login, connect your hardware wallet to your computer and open Trezor Suite. The Trezor Login process involves entering your PIN, passphrase if enabled, and verifying actions directly on your device for added protection.
Why Trezor Login Security is Essential
Protecting your funds during Trezor Login is critical. With every Trezor Login, the hardware wallet ensures private keys never leave the device, reducing risks of hacks or phishing attacks commonly associated with online wallets.
Common Trezor Login Issues and Fixes
Some users experience problems during Trezor Login, such as browser connectivity issues or PIN entry errors. Updating firmware, clearing browser cache, or reinstalling Trezor Suite often resolves these Trezor Login challenges quickly.
Top Tips for a Smooth Trezor Login
- Always download Trezor Suite before performing a Trezor Login.
- Keep your firmware updated to prevent Trezor Login errors.
- Use a secure USB connection during your Trezor Login.
- Enable passphrase protection for every Trezor Login session.
- Verify all actions on the hardware device during Trezor Login.
Trezor Login for Advanced Users
Advanced investors using Trezor Login often enable features like Shamir Backup, hidden wallets, and integration with third-party apps. Each Trezor Login provides maximum flexibility while still prioritizing cryptographic security.
Trezor Login on Multiple Devices
A Trezor Login can be performed on both desktop and web environments. While desktop Trezor Suite offers the full experience, browser-based Trezor Login allows convenient access, as long as you remain connected to the hardware wallet.
Conclusion: Secure Your Assets with Every Trezor Login
In conclusion, every Trezor Login is designed to balance ease of use with industry-leading security. By following best practices, troubleshooting common issues, and enabling advanced features, Trezor Login becomes the most reliable method to safeguard your cryptocurrency portfolio.